-
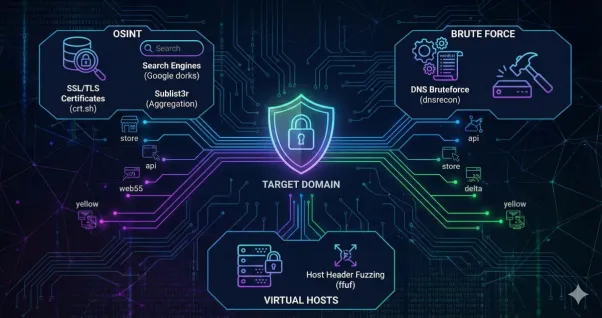 Subdomain Enumeration | TryHackMe Write-up
Subdomain Enumeration | TryHackMe Write-upComplete walkthrough for Subdomain Enumeration TryHackme room. Learn the various ways of discovering subdomains to expand your attack surface of a target.
3 min -
 Content Discovery | TryHackMe Write-Up
Content Discovery | TryHackMe Write-UpTryHackMe write-up for “Walking An Application.” Learn how to use browser developer tools to manually discover hidden flags and potential vulnerabilities.
5 min -
 Fixing WSL Ubuntu Setup & Hostname Issues
Fixing WSL Ubuntu Setup & Hostname IssuesStep-by-step guide to install Ubuntu on WSL, fix hostname errors, and an honest comparison between WSL and Kali in VirtualBox.
3 min -
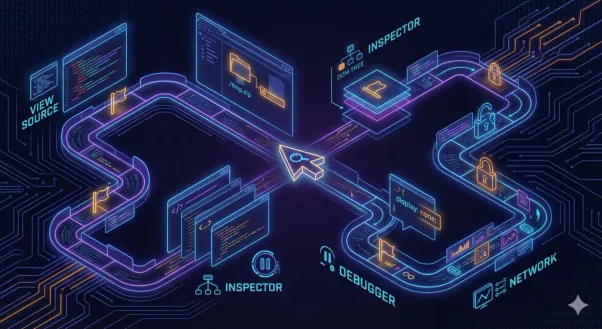 Walking An Application | TryHackMe Write-Up
Walking An Application | TryHackMe Write-UpHands-on walkthrough of Walking An Application on TryHackMe, exploring source code, Inspector, Debugger, and Network tools to uncover hidden flags.
5 min -
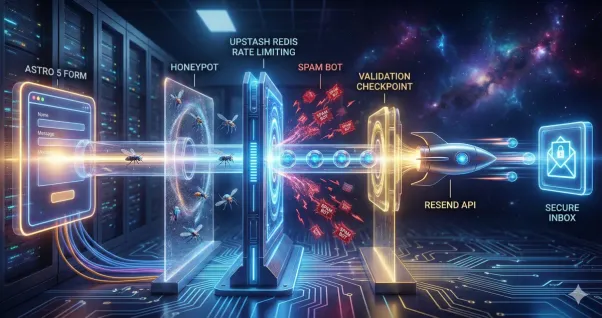 Secure Astro 5 Contact Forms with Resend and Upstash
Secure Astro 5 Contact Forms with Resend and UpstashBuild a production-ready contact form in Astro 5. Learn to integrate Resend for emails and Upstash Redis for rate limiting to block spam effectively.
5 min -
 Designing a MySQL Database for B2B Energy Products
Designing a MySQL Database for B2B Energy ProductsDesign a basic product data for B2B electrical and renewable energy products with tier pricing, categories, brands, and multi-currency support.
5 min -
 OWASP Top 10 2025: Insecure Data Handling | TryHackMe
OWASP Top 10 2025: Insecure Data Handling | TryHackMeHands-on walkthrough of Cryptographic Failures, Injection, and Integrity Failures in OWASP Top 10 2025 using TryHackMe labs.
3 min -
 Self-Control Is the First Leadership Test
Self-Control Is the First Leadership TestBefore leading others, master yourself. In a world built to hijack attention, discipline over impulse is the foundation of trust and true authority.
3 min
Blog
Page 3 - Showing 8 of 95 posts
View all posts by years →